The deceptive methods of adware infiltration
The recent investigation has shown that advertising-supported applications (adware) are very prevalent nowadays. These programs tend to enter the system without users’ consent; however, it does not mean that they cannot download and install adware themselves. The reason why so many computer users install this type of undesirable program onto their computers is the fact that adware often pretends to be very beneficial software. The truth is that these applications are mainly published to promote products and services, generate revenue for the publishers, and drive traffic to particular websites. On top of that, their presence might result in the entrance of different kinds of malicious software. Thus, computer users should be aware of the fact that adware is not the type of software that should be kept on the system.
A number of companies throughout the world publish advertising-supported applications these days. Some of the best known ones are Web LLC and Simply Tech Ltd. Even though the publishers might differ, all adware programs act in a similar way. Computer users whose systems are infected with adware will definitely suffer from different kinds of advertisements that will appear in a form of banners, in-text, interstitial, search-related, video, and pop-up ads. In most cases, these advertisements are very intrusive and thus tend to disrupt browsing sessions, not to mention the fact that they might expose computer users to malicious software. In some cases, advertisements are shown in order to recover development costs; however, authors tend to use them as tools to receive money from pay-per-click websites more frequently.

As there is a huge possibility to infect the system with adware these days, it is very important to be aware of their main methods of entrance in order to be able to prevent this unwanted software from entering the system. According to recent research, advertising-supported applications usually travel bundled with free programs, also known as freeware. Different kinds of software that can be categorized as freeware are accessible for a wide range of users; thus, it is not surprising that adware is one of the most commonly detected infections. Computer users have to be especially careful when installing freeware (e.g. PDF recorders, video streamers, and various system optimization tools) because careless installation might result in the entry of adware programs, especially those published by Super Web LLC, Kimahri Software Inc., and Innovative Apps. In addition, it is advisable to download software from official websites only.
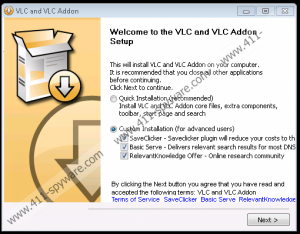
Another method of adware distribution involves tricking computer users into clicking on deceptive advertisements. They might offer to install the necessary updates or missing software, e.g. Java or Flash Player; however, the truth is that computer users will install advertising-supported applications and, probably, other kinds of malware. In addition, computer users might also come across pop-ups that seem as regular Windows notifications. It does not matter whether they will click on Yes or No buttons, which tend to be presented in the fake notification, an automatic download of adware will start. In some cases, tracking technologies are used to present the relevant content as well. This tactics helps to lure computer users into downloading unreliable applications. Those who seek to protect their systems from various kinds of infections, including adware, should always ignore suspicious ads appearing on random websites and install new software with a great care.

Even though there are several ways of adware distribution, it does not mean that computer users cannot download and install them consciously. The majority of advertising-supported applications pretend to be very useful software; they often claim to be able to enhance browsing experience, change the way people surf the web and search for the information as well as help save money and time on various merchandise websites. Unfortunately, computer users notice that their systems have started acting suspiciously after installation of adware. Some of them delete the program straightaway, while others decide to keep the software and adapt to these undesirable activities. Security specialists of 411-spyware.com do not recommend doing that because they have observed that adware programs tend to act behind the back as well, for example, connect to the internet without permission and record data regarding users’ activities on the web like visiting various websites, entering search queries into the search box, and accessing particular content.
![]()
The removal of advertising-supported applications will not only stop all those undesirable activities, but also help computer users to protect their systems from even more serious malware. Unfortunately, it is not always very easy to detect and remove adware because they tend to hide on the system and pretend to be very beneficial. In order to detect and remove adware easily and quickly, it is advisable to scan the system with an antimalware tool. The licensed version of this security tool will make sure that you will not have to worry about the security of your system in the future. Of course, it is also possible to remove adware manually (please find the instructions below); however, this method is not suitable for those that do not have experience in malware removal.
The removal of an advertising-supported application
Windows XP
- Open the Start menu.
- Select Control Panel.
- Click Add or Remove Programs.
- Select the adware program and click Remove.
Windows 7 and Vista
- Click the Start button to open the menu.
- Select Control Panel.
- Access Uninstall a program.
- Right-click on the suspicious application.
- Select Uninstall to confirm the removal.
Windows 8
- Tap the Windows key.
- Right-click on the background and select All apps.
- Find Control Panel on the list and select it.
- Click Uninstall a program.
- Find the undesirable program on the list.
- Right-click on it and then click the Uninstall button.
Internet Explorer
- Open the browser.
- Tap Alt+T.
- Select Manage Add-ons.
- Click Toolbars and Extensions.
- Locate the suspicious extension and select it.
- Click Disable.
Mozilla Firefox
- Open your browser.
- Tap Ctrl+Shift+A.
- Select Extensions from the menu on the left.
- Find the extension that needs to be removed and select it.
- Click the Remove/Disable button.
Google Chrome
- Launch your browser.
- Tap Alt+F to access the menu.
- Select Tools and then move to Extensions.
- Select the extension that you wish to erase.
- Click the recycle bin button.
- Click Remove in the dialog box.

