Hacked Ransomware Removal Guide
Ransomware is one of the biggest cyber threats in this digital age, and new attacks are launched one after another. The Hacked ransomware is another dangerous computer infection that encrypts a variety of files in an attempt to obtain your money. Under any circumstances should you ever pay the sum required by the ransomware, because it is hardly possible that you will get your files restored. The key goal of cyber attackers is to lure you into paying the money requested. When the Hacked ransomware corrupts your file, your key goal is to remove the infection from the computer, and, without a doubt, take preventative measures to protect yourself from similar danger in the future.
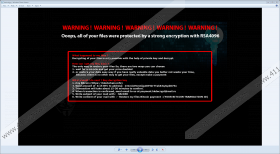
The Hacked ransomware is also known as Trojan.Win32.Filecoder, Trojan.Cridex, Exploit.Win32.BypassUAC.drv, and a variant of Win32/Fildercoder.NNH. If you look closer at the user interface of the Hacked ransomware, you are likely to notice that the infection is similar to the interface of the infamous WannaCry ransomware, which has caused a lot of damange in over 100 countries.
This Hacked infection spreads in several ways. It can arrive at your PC as a malicious spam email attachment; moreover, it can get access to your device through RDP configurations. In order to prevent the Hacked infection and many other threats, it is essential that you keep your operating system shielded by a powerful malware and spyware removal tool. Visiting unsafe websites and downloading unknown software may also result in malware installation, so you should be aware of the dangers that you might be expossed to when using a Internet-connected device.
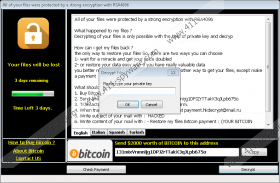
Once on the computer, the Hacked infection changes the background of the desktop and drops a ransom note in a .txt file named How_to_decrypt_files or @readme_English.txt. The text of the ransom note is also visible on the screen. The infection has also been found to drop ransom notes written in Italian, Spanish, and Turkish. After encrypting files, the infection changes filenames by adding a new extension .hacked, which is appended next to the existing extension.
The Hacked ransomware is coded to encrypt files using RSA encryption, which requires two different but linked keys – public and private keys – one of which is used to encode information, whereas the second one is used to decrypt it. This is called asymmetric encryption and is used widely to ensure secure data transmission and storage. The strength of encryption depends on the key length, which is reflected in the name of the algorithm; for example, 1024-bits long. The 4094-bits RSA key was also used by the TeslaCrypt and CryptXXX ransomware strains. This code is uncrackable, and the only way to restore your files is to take out the hidden hard drive containing backups of your data.
According to the ransom note, victims have to buy Bitcoins and send the sum required to the address given. Interestingly, in the instructions displayed, victims are required to send attackers 0.5 BTC, whereas at the very bottom of the ransom window, the sum of $2,000 in Bitcoins is given. In any case, you should not purchase the decryption key because you are likely to remain deceived. Nobody can guarantee that you will be able to access your files after submitting this hefty fee to the unknown recipients.
The infection attempts to prod victims into taking action by warning them that an attempt to decrypt files with an incorrect key ends in file destruction. This is just another try to hurry you to pay the ransom, but you should not trust the infection. Remove it from the computer and make sure that you keep your OS and software updated.
When it comes to removal, you can try terminating the infection manually, which you can do by deleting suspicious recently downloaded files. Without a doubt, it is much safer to run a system scan of a powerful malware and spyware prevention program. Our recommended security tool can identify and remove the Hacked ransomware and also fight off many other threats that attempt to access your PC. The sooner you take action, the sooner you will get protected, so do not wait any longer.
Remove the Hacked ransomware
- Delete all of the malicious files from the desktop.
- Access the Downloads folder and look for questionable files.
- Check the Temporary folder for unreliable files.
- Empty the Recycle bin.
Hacked Ransomware Screenshots: