Decryption Assistant Ransomware Removal Guide
Decryption Assistant Ransomware is part of the Hidden-Tear ransomware family. It is still in development, but its creators decided to release it unfinished, probably for testing purposes. Allegedly, it uses the AES encryption algorithm to encrypt many of your file formats, but the good news is that it does not encrypt your files as it is still in development. Therefore, you can remove this ransomware without suffering any consequences. Still, it will be completed at some point. Therefore, we think it is important to provide you with as much information about this ransomware as possible because it can morph into a serious computer infection in the near future.
We have managed to obtain a sample of this ransomware’s main executable that was named as FlashPlayerUpdate.exe. Clearly, it was disguised as a Flash Player update to compel would-be victims to run the installer. If this ransomware happens to infect your PC, then it will not do anything to your files but, theoretically, this ransomware could encrypt them with a unique AES encryption algorithm. Our research has revealed that it can encrypt .asp, .aspx, .csv, .doc, .docx, .exe, .html, .jpg, .mdb, .odt, .php, .png, .ppt, .pptx, .psd, .sln, .sql, .txt, .xls, .xlsx, and .xml file extensions. As a result, many of your documents, applications, and other content would become unavailable. The encrypted files would be appended with the ".pwned" file extension.
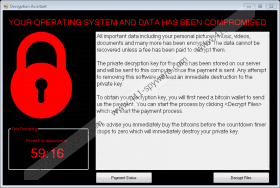
At its current state, however, this program does neither encrypt nor append the files in order to demand that you pay a ransom. We have found that this particular ransomware would require you to pay the ransom in Bitcoins, but the amount is not specified. In the event the encryption is complete, and even at its current stage, Decryption Assistant Ransomware opens its GUI with a ransom note and a timer that is set to run out in one hour. The ransomware developers would use scare tactics to compel you to pay the ransom. They say that you have one hour to pay the ransom or the decryption key will be deleted. However, we have no information on whether the server that is supposed to host the decryption key is online. Therefore, you should not pay the ransom, and you could not pay it even if you wanted as the “Decrypt Files” and “Payment Status” buttons in the ransomware GUI do not work.
While there is no information on how Decryption Assistant Ransomware is distributed, we believe that its creators must have set up an email server that sends this ransomware to random email addresses, but we have also received some clarifying information which stated that this ransomware targets people from English speaking countries. While the sample we tested was named FlashPlayerUpdate.exe, we assume that it is unlikely that this same file is sent via email. There must be variations of the name, and it is likely that the iteration with the name FlashPlayerUpdate.exe was most likely distributed on malicious free distributing websites and possibly torrent websites.
That is all of the information we currently have on this ransomware. As you can see, it is currently harmless, but it has the potential to become one serious computer infection that can inject your PC secretly and encrypt many of your personal files in order to extract money from you. If your PC has become infected with the unfinished version of Decryption Assistant Ransomware, then you should consider yourself lucky and remove it as fast as you can. We have included a manual removal guide below, but you can also use an antimalware program such as SpyHunter to delete it for you.
Delete the ransomware manually
- Press Win+E keys.
- Type the following file paths in File Explorer’s address box and press Enter.
- %TEMP%
- %USERPROFILE\Downloads
- %USERPROFILE\Desktop
- Locate this ransomware (e.g. FlashPlayerUpdate.exe,)
- Right-click it and click Delete.
- Empty the Recycle Bin.
Decryption Assistant Ransomware Screenshots: