Privacy Protection Removal Guide
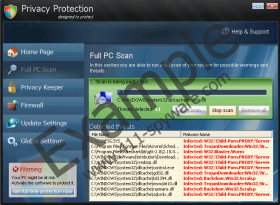
The developers of Malware Protection rogue antispyware have been hard at work with the release of Privacy Protection – their latest rogue application released in November 2011. This rogue antispyware application does a great job at imitating the workings of a real antispyware application, even offering supposed help and support to their users. The Privacy Protection rogue has a well-designed user interface designed to look authentic and gain its victim’s trust. It will profess to offer a full PC scan, as well as update the firewall and maintain the PC’s privacy.
Privacy Protection will not alert the user to its presence on the system immediately. It will only reveal its presence to the user once it managed to securely root itself in the system. Once this happens the rogue will initiate a fake security scan of the system and inform the user that his PC is under attack. It will inform the user that the only way to stave off this attack will be to purchase a Privacy Protection license and activate the rogue on the system. Once the user does this the fake scan will report that all threats have been eliminated, but that is not true and all forms part of Privacy Protection’s attack on the system.
Users will also find that they are unable to establish a connection to the Internet, and cannot launch applications on the infected PC. This is done to further annoy and panic the user into thinking his PC is under attack. It is also done to prevent the user from running or downloading any application which could possibly detect and remove Privacy Protection from the system. Each time the user attempts to execute an application he will receive a message similar to the following fake alert:
Calc.exe cannot start
File calc.exe is infected by W32/Blaster.worm. Please activate Privacy Protection to protect your computer.
As a further attack against the system Privacy Protection will spam the user with numerous falsely generated security threats, informing him of the same thing:
Security Warning
Malicious program has been detected. Click here to protect your computer.Firewall Warning
Hidden file transfers to remote host has been detected.
has detected a leak of your files through the Internet. We strongly recommend that you block the attack immediately.
Other symptoms associated with this infection range from increased erratic system behavior to poor system performance. Certain system folders and its contents will also be hidden from the user and random desktop items will be generated and deleted to further confuse the user and any installed security software.
In order to protect the PC against the damage this rogue will cause, and to restore its protection, security and privacy users are urged to destroy Privacy Protection immediately. This can be safest achieved by making use of a powerful security tool which will not only erase Privacy Protection but also protect against similar attacks in future.
Privacy Protection Screenshots: