Yoshikada Ransomware Removal Guide
If Yoshikada Ransomware invades your operating system, and you do not remove it right away, it quickly encrypts your files to hold them hostage. The goal behind this is to make you pay a ransom. The threat does not make a concrete demand right away, and, instead, it requests you to communicate with cyber criminals by emailing them at yoshikada@cock.lu. Needless to say, we do not recommend contacting cyber criminals or paying the ransom. Communicating with them can be dangerous because they could expose you to additional malware. Also, they could record your email address and use it to scam you in the future. If you pay the ransom, cyber criminals would definitely accept it, but it is unlikely that they would give you a file decryptor in return. In fact, we are sure that you would not be given it. Are your personal files backed up? If they are, you do not need to worry about losing personal data permanently. Even if they are not backed up, and you end up losing files, you must delete Yoshikada Ransomware.
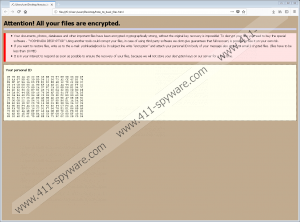
What’s with the “.crypted_yoshikada@cock_lu” extension that is added to your personal files? This extension might be the first thing that reveals the existence of Yoshikada Ransomware for you. When this ransomware encrypts files – which it does using a complicated algorithm that cannot be cracked – it attaches a unique extension to mark the corrupted files. This is something that most ransomware threats do, including MindLost Ransomware, Desucrypt Ransomware, or Lime Ransomware. In many cases, the extensions are generic – such as “.locked” – but the one created by Yoshikada Ransomware is, of course, very unique. It represents the email address that you are meant to contact cyber criminals via. The same email is also revealed using the “how_to_back_files.html” file. The name of the file has nothing to do with the message represented via it because it does not show how to back up personal files. Instead, it presents information that, supposedly, is meant to help you decrypt files. According to the ransom note, you have to email yoshikada@cock.lu and then purchase the so-called “YOSHIKADA DECRYPTOR.” Instead, you should remove the ransom note and then move on to delete the ransomware itself.
Besides worrying about the decryption of data and the removal of Yoshikada Ransomware, you also need to worry about your virtual security. Since this ransomware has slithered in and corrupted files without any warning, it is possible that other infections have found their way into your operating system too. It is most likely that you let Yoshikada Ransomware in by opening a corrupted spam email attachment, but if your system is unguarded, this is just one of the many security backdoors that could be exploited to drop malware onto your operating system. Protecting the system is crucial in any situation, and only if you set up a reliable security system will you evade malware in the future. That is not all. You also need to think about your files. If the system is guarded, your files should be safe; however, just to be extra careful, you should back up your files externally. If you take care of that, you will never lose your files even if they are corrupted or are lost due to technical issues. Please do not forget about this after the removal.
Can you handle the steps shown below? If you are not experienced, they might seem quite complicated, but you should be able to remove Yoshikada Ransomware on your own. Obviously, if other threats exist, you will need to take additional steps to eliminate them too. Are you overwhelmed, and you do not know how to protect your operating system hereafter? If that is the case, we strongly recommend installing a legitimate anti-malware program to take care of it all. This program will delete Yoshikada Ransomware and other threats if they exist, and it will also establish full-time protection so that you would not need to worry about other threats in the future. Do you have any questions? We welcome all of them in the comments section. Post your comment, and our research team will try to get back to you as soon as possible.
How to delete Yoshikada Ransomware
- Tap keys Win+E to launch Explorer.
- Type %APPDATA% into the bar at the top and tap Enter.
- Delete the {unique name}.exe file that is the launcher of the ransomware.
- Tap keys Win+R to launch RUN and then enter regedit.exe into the dialog box.
- In Registry Editor go to HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce.
- Delete the value named BrowserUpdateCheck (first check the value data to see if it represents the %APPDATA%\{unique name}.exe file deleted in step 3).
- Empty Recycle Bin and then right away install a malware scanner to inspect your system for leftovers.
Yoshikada Ransomware Screenshots: