Ranion 1.08 Ransomware Removal Guide
New file-encryptors continue popping up, and the latest to join the party is Ranion 1.08 Ransomware. The number included in the name of this threat is not completely random. Our research team has found that this malware was created using a builder that is publically available, and other infections have been created using it in the past. One of them is known as Ranion 1.07 Ransomware. Other versions exist too. It is hard to say how the creators of these threats can distribute them because different methods can be employed. In most cases, spam emails with corrupted attachments and links and employed, but the malware could be distributed in other ways as well. Once the infection is in, it can create files and registry entries without alerting the victim, and the encryption of files is then performed in a silent manner as well. Unfortunately, once files are encrypted, it is unlikely that anything can be done to recover them. In any case, you need to delete Ranion 1.08 Ransomware, and we are here to help you with that.
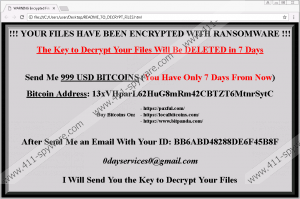
When Ranion 1.08 Ransomware gains access to your operating system, it creates a copy. The name of this file is unique, and it always includes the date and time it was created. The infection does not run using the copy, but, most likely, it could be used if you removed the original launcher file. The copy is placed in the %PUBLIC% directory, which is also where you can find one of the two ransom note files. The other one is placed on the Desktop, and both are called “README_TO_DECRYPT_FILES.html.” The message within the file pushes the victims of Ranion 1.08 Ransomware to pay a ransom of $999. The sum must be transferred in Bitcoins to a special wallet (13xVHparL62HuG8mRm42CBTZT6MtnrSytC), after which, an ID revealed via the ransom note must be sent to 0dayservices0@gmail.com. If these steps are fulfilled, a decryption key is then given to recover files. This all might seem great, and you might even be willing to pay that much to get your files back; however, the reality is that the promises made by cyber criminals should never be taken seriously. Unfortunately, you are unlikely to receive a decryptor and recover your files even if you do as told. You should also pay no attention to the threat that your files would be deleted if you did not pay the ransom.
The creator of Ranion 1.08 Ransomware cares about nothing else but money; otherwise, they would not have created this malicious infection. To push the victims into giving in and paying a huge sum, they take files hostage, and, if the files are not backed up, the victim is pushed into a corner. This would not be an issue if files were backed up. If you are not using backups, you need to start doing it as soon as you remove Ranion 1.08 Ransomware from your operating system. Besides the hundreds of malicious ransomware threats that could target your personal files, you also need to think about other dangerous threats that could affect your personal data. Some of them could delete files, and others could leak them online, which, of course, you do not want. You also need to think about the possibility of experiencing hard drive damage, which could also lead to the loss of data. Your computer could also be stolen. Basically, there are plenty of reasons for you to set up a file backup, and if you do not want to invest in an external drive, you can look into cloud storage. Of course, first, you need to remove the malware that is running wild on your PC.
Points of execution exist in windows Registry at HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run and HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run. You need to delete them. You also need to remove Ranion 1.08 Ransomware launcher and its copy. These steps can be quite complicated, especially if you are inexperienced, which is why employing anti-malware software is strongly recommended. Note that if you install it, you will not need to worry about the protection of your operating system as well, which is very important if you want to keep ransomware and other kinds of malware away in the future. If you take care of that and back up your personal files, you will not need to fear file encryptors.
How to delete Ranion 1.08 Ransomware
- Launch Task Manager (tap Ctrl+Shift+Esc) and right-click the malicious process (you need to be completely sure that this process is malicious before you move on).
- Select Open file location, go back to the Task Manager, and End Process.
- Right-click the malicious .exe file in the opened location and then select Delete.
- Type %PUBLIC% into the bar at the top of the Explorer.
- Right-click and Delete the copy .exe file of the ransomware (e.g., r44s_2018-03-05 0712.exe).
- Right-click and Delete the file named README_TO_DECRYPT_FILES.html.
- Move to the Desktop and repeat step 6.
- Launch Registry Editor (tap Win+R to launch RUN and then enter regedit.exe into the dialog field).
- Navigate to HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run.
- Right-click and Delete the value called Message-2018.
- Navigate to HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run.
- Right-click and Delete the values named Message-2018 and Backup-2018.
N.B. Install a legitimate malware scanner and run a full system scan to check if your system is clean.
Ranion 1.08 Ransomware Screenshots:
Ranion 1.08 Ransomware technical info for manual removal:
Files Modified/Created on the system:
| # | File Name | File Size (Bytes) | File Hash |
|---|---|---|---|
| 1 | README_TO_DECRYPT_FILES.html | 897 bytes | MD5: be8a4cbb2a7ec9e1d74f454b77a91c6d |
| 2 | r44s_2018-03-07 0205.exe | 281088 bytes | MD5: eca948ea4dec7a9237605658e516baa6 |
Memory Processes Created:
| # | Process Name | Process Filename | Main module size |
|---|---|---|---|
| 1 | r44s_2018-03-07 0205.exe | r44s_2018-03-07 0205.exe | 281088 bytes |

