Maykolin Ransomware Removal Guide
If your personal files were corrupted by Maykolin Ransomware, you will find a file called “crypt0.txt” on the Desktop. This file lists the files that were encrypted by this dangerous infection. There is another file that provides users with more information, but it is concealed. This file is called “info.html”, and you can find it in the %WINDIR% directory. This file represents the demands that the creator of the ransomware has for you in return of a decryption key. The problem is that we cannot confirm that this tool exists, and we definitely cannot confirm that this tool would be provided to you if you paid money for it. If you look at other ransomware infections, it is unlikely that you would get anything in return. After all, the people who create these ransomware threats are malicious, and if they cared about your files or your wellbeing, they would not create malware in the first place. If you continue reading, you will learn how to delete Maykolin Ransomware from your operating system manually, as well as what you should do beforehand.
Have you discovered that your files got corrupted soon after you opened a suspicious spam email attachment? According to our research, this infection is usually introduced to victims using spam emails, and so it is most likely that this is how it has entered your operating system as well. Once this threat is in, it creates a RUN entry in the Windows Registry to ensure that it starts running when you restart the PC. By setting this up, the infection ensures that the new files you might place on the infected computer are infected as well. Due to this, if you have backups of the encrypted files, you should replace the corrupted copies only after you remove Maykolin Ransomware. Unfortunately, if you do not have backups stored on, let’s say, external drive, you are unlikely to be able to recover your files. It was found that the malicious Maykolin Ransomware creates a unique AES file for each file individually, and both AES and RSA keys are used to encrypt them. RSA-4096 encrypts the first 300 bytes, and the unique AES key takes care of the remaining bytes. This is what you can call a strong encryption.
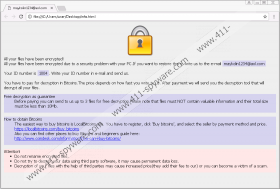
Were you introduced to the info.html file, or did you learn about it from us? This HTML file was created by Maykolin Ransomware to introduce you to the ransom payment instructions, but, surprisingly, it is not opened automatically. This means that once the ransomware slithers in, the user does not know what is happening. According to the information in the HTML file, you need a decryption tool to have the files decrypted, and to obtain it, you are expected to pay a ransom. The sum of the ransom is not specified, and there are no details regarding the payment. Because of that, an email address (maykolin1234@aol.com) is attached. If you email cyber criminals, they are most likely to provide you with instructions on how to pay a ransom. Even if the payment is small, you have to remember that Maykolin Ransomware was created by cyber criminals, and so the promises that follow this threat are most likely to be empty. If, by some miracle, you are provided with a decryption tool that restores your files after paying the ransom – you should not rely on this to happen – you have to remove the ransomware anyway!
If your files in the %USERPROFILE% directory and all subfolders were encrypted by Maykolin Ransomware, there is not much you can do. Even if you delete this ransomware successfully – which is what you must do in any situation – your files will remain locked. Unfortunately, it is quite unlikely that anything will change even if you pay the ransom that is requested via the clandestine info.html file. In the best case scenario, all of your personal files are securely backed up, and you can replace the infected copies with the backup copies as soon as you remove Maykolin Ransomware from your operating system. The removal of this malware can be difficult if you cannot find and erase the main launcher file. If you are unable to get rid of this threat manually using the instructions below, consider employing anti-malware software. Do not forget that this software can also provide you with reliable full-time protection, which is what you need with so many dangerous threats emerging every day.
How to delete Maykolin Ransomware
- Identify the malicious launcher file, right-click it, and choose Delete.
- Tap Win+E to access Explorer.
- Type %WINDIR% into the bar at the top and then tap Enter.
- Right-click the file named info.html and select Delete.
- Tap Win+R to launch RUN.
- Type regedit.exe and click OK to launch Registry Editor.
- Navigate to HKCU\Software\Microsoft\Windows\CurrentVersion\Run.
- Right-click the value named systems and click Delete. Check if it is linked to the malicious .exe file first.
- Perform a full system scan to check if your operating system is now clean.
Maykolin Ransomware Screenshots: