Kryptonite Ransomware Removal Guide
Kryptonite Ransomware is a malicious application which usually arrives on computers next to a simple snake game users willingly download from the web. Undoubtedly, they do not know that they have downloaded a game bundled with a crypto-threat until they find out that files with .png, .jpg, .bmp, .mp4, .drw, .indt, .ptb, .css, .zipx, .tar, .7z, .wma, .mov, .txt, .pdf, and a bunch of other extensions can no longer be opened. Unlike other ransomware-type infections, Kryptonite Ransomware does not change the original extensions of these encrypted files, so not all the users soon realize that their files have been encrypted. They usually first notice a new image set as Desktop background and a file Ransome Note.txt created on their Desktops. Additionally, in some cases, they hear a voice message played for them automatically – it tells users what the reason behind the inability to access personal files is. Users who become victims of this nasty infection should go to delete it from their systems the first thing after realizing that it is inside their PCs instead of going to pay a ransom it requires. Specialists at 411-spyware.com say that users should never pay cyber criminals money no matter how badly they need those encrypted files. We are well aware of the fact that your important files have been encrypted, but we also know that you might not get the key for unlocking files from cyber crooks. Instead, they might take your money and then go to release a new ransomware infection.
Kryptonite Ransomware is an infection encrypting files, as you must already know; however, it does not encrypt all files it finds located on victims’ computers. Research carried out by our specialists has shown that it leaves files located in certain directories untouched, for example, we can assure you that you will find files in directories having words ~BT, Boot, metadata, history, chrome, cache, Windows, etc. in their names intact. It seems that it is not going to ruin your PC and certain programs; however, it will definitely lock your pictures, music files, videos, and documents without mercy. As the ransom note Ransome Note.txt left for users on Desktop tells, files can only be restored by paying $500 to cyber criminals. Users are also told to disable their Windows firewalls. Do not do any of these activities because, in the first case, you will be left without money and without files. In the second case, disabling the firewall might result in the entrance of more harmful threats. You can recover your files for free only from a backup. In case you have never backed up your files, remove Kryptonite Ransomware from your PC and wait till specialists develop a free decryption tool. This might take a while.
Ransomware infections slither onto computers with the intention of encrypting users’ files and then extracting money from them. Kryptonite Ransomware is no exception, but it does not perform this only activity on victims’ computers. It has also been noticed that it makes several other modifications following the successful entrance. As mentioned at the beginning of this article, it changes a Desktop wallpaper and creates a new .txt file on Desktop with a ransom note. What is more, thorough analysis has shown that it creates its own registry key HKCU\SOFTWARE\security\Kryptonite and drops three new files, awsomeRansome.jpg , 1.exe, and 1.jpeg in %APPDATA%. The first file is a picture this ransomware infection sets as Desktop background, whereas two other files are the ransomware infection itself. It has also been noticed that the 1.exe file periodically connects to the server 52.225.217.31:27015. Judging from a number of changes it applies, it is quite a sophisticated malicious application; however, we have no doubts that you will delete it yourself one way or another.
Delete Kryptonite Ransomware as soon as possible if you do not want this infection to encrypt new files you create. Unfortunately, already encrypted files will not be unlocked for you even if you erase this infection. Since it is quite sophisticated malware which might revive at any time, you must delete it fully. That is, you cannot leave a single component of this threat on your PC. Therefore, we suggest performing the removal steps indicated in our manual removal guide (see below). Alternatively, this infection can be deleted automatically. Unfortunately, an automated malware remover will not unlock those already encrypted files for you either.
Kryptonite Ransomware removal guide
- Open the Registry Editor (tap Win+R, type regedit, and click OK).
- Open the HKCU\Control Panel\Desktop registry key and locate the WallPaper Value there.
- Right-click on it and select Delete.
- Move to HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Wallpapers.
- Delete the BackgroundHistoryPath0 Value.
- Open the Run registry key HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run.
- Delete the Value having . as its name.
- Remove the Value with the name . from HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce as well.
- Close the Registry Editor.
- Press Win+E.
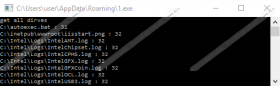
- Go to %APPDATA%.
- Remove these three files:
- 1.exe
- 1.jpg
- awsomeRansome.jpg
- Delete all recently downloaded files from %TEMP%, %USERPROFILE%\Desktop, and %USERPROFILE%\Downloads.
- Remove Ransome Note.txt from %USERPROFILE%\Desktop.
- Clear the Recycle bin.
Kryptonite Ransomware Screenshots: