Computeren er Blevet Blokeret Virus Removal Guide
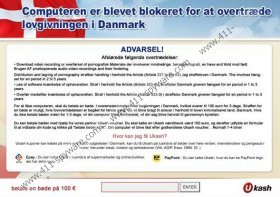
Computeren er Blevet Blokeret virus is a computer threat which we categorize as a ransomware virus because it disables access to the system and displays a bogus ransom message claiming that you have committed some crimes, which is why a fine of 100 euros is imposed on you. The message should not be trusted because of its content and criminals behind. They created this threat to deceive you into paying the money, so do not help them to earn money and remove Computeren er Blevet Blokeret virus.
The infection is also called Ukash virus because the payment method which is provided by the virus is Ukash. This service is present by other ransomware infections, too, including El Equipo ha Sido Bloqueado virus, Federal Department of Justice and Police Virus, Internet Crime Complaint Center Virus, and others. All of them attempt to deceive computer user by displaying false accusations that are said to be provided by a particular institution, for example, police. However, in the case of Computeren er Blevet Blokeret virus only the articles of law are presented:
Distribution and lagring of pornography strafbar handling i henhold the Article (Adele 227 to the 23) Jeg straffeloven i Danmark. The involves fæng-sel for en period in 2 til 5 years.
use of software krænkelse of ophavsretten Straf i henhold the Article (Article 323-2) i straffelov Danmark giveren fængsel for en period in 1 to 3 years.
Overfør mediefiler krænkelse of ophavsretten. Straf i henhold the Article (Article 323-3) i straffelov Danmark giveren fængsel for en period in 1 to 3 years.
Do you want Computeren er Blevet Blokeret virus to remain within the system even after you pay the ransom? If the answer is negative, remove the infection without hesitation. At this point you should know that it is essential to use a reliable spyware removal tool; hence we suggest that you use SpyHunter. This spyware removal tool can delete infections and protect the system against ones in the future. Find our guidelines below to find out how to install the tool and remove the virus:
Window Vista/7:
- Reboot the computer.
- Wait until the BIOS screen (information on hardware) disappears and start tapping the F8.
- Use arrow keys to select Safe Mode with Networking and press Enter.
- Go to http://www.411-spyware.com/download-sph and download SpyHunter.
- Install it and launch a program to have the virus detected and removed.
Windows XP:
- Restart the PC.
- Start tapping F8 as soon as the BIOS screen disappears.
- Select Safe Mode with Networking by using the arrow keys on the keyboard. Press Enter.
- Click on Yes in the dialog box.
- Open the Start menu.
- Launch Run.
- Type “msconfig” in the box and press OK.
- Click on the Startup tab and uncheck all startup entries.
- Press Apply.
- Close the windows and download SpyHunter.
- Restart the computer and install the file downloaded.
- Run a system scan to detect and remove the infection.
Computeren er Blevet Blokeret Virus Screenshots: