Bud Ransomware Removal Guide
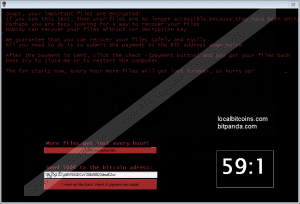
Finding that your computer has just been infected by ransomware could be infuriating, especially when you find a threatening warning being typed in a separate window. The Bud ransomware is one of the threats that can easily take your files hostage, and once it does so, it demands that you pay a ransom of 500 Euros, implying that the infection targets Europe-based computers. The Bud ransomware does cause damage, but its requirement to pay up should be disregarded. The attackers guarantee that you will regain access to your encrypted files, but the odds are that they will not bother providing you with the decryption key or decryption tool. You should focus on the removal of the Bud ransomware, and if you are eager to find out how to remove this threat, move down to the end of the review to find a removal guide.
The Bud ransomware can spread in several ways, including emails and their compromised attachments, but it is assumed that the major way of distribution is unsecured Remote Desktop Protocol (RDP) settings. In any case, taking preventative measures is highly recommended because different types of infections have their ways of spreading. It is important that you bypass free software sharing websites and networking, disregard questionable pop-up ads and banners, and connect only to secured networks. On top, implementing a reputable anti-spyware program is also highly important. At some point you might fail to identify a dangerous situation, so it is worth considering installation of anti-malware software.
The Bud ransomware easily encrypts files on unprotected computer by using the AES encryption method. AES encryption is a commonly encountered method of data coding used by the US government and other institutions to safely store and transfer information. AES encryption is symmetric encryption, meaning that for encoding and decoding data a single key is used. This type of encryption is regarded as one of the simplest type of encoding but that does not mean that you are likely to break the code. Instead of wasting your time and energy, remove the Bud ransomware from your computer and back up your data from a storage device or a backup storage cloud.
When analyzing the Bud ransomware, it has been found that this threat creates two copies of itself in the folders LOCALAPPDATA and APPDATA. More specifically, the files of the infection can be found in %LOCALAPPDATA%\Corel\CorelCGS.exe and %APPDATA%\Corel\RegisterCGS.exe, the latter of which is not active. Additionally, the threat has its point of execution the pathname of which is HKCU\Software\Microsoft\Windows\CurrentVersion\Run::RegisterCGS.exe. This configuration is created so that the infection starts running at you log into the system. Encrypted files immediately get the new extension .bud, hence the name of the infection. It has also been noticed that after restarting the computer, it might not work as usual because the threat disables the Windows Program Manager, also known as Windows Explorer, the file of which is explorer.exe. Additionally, the Task Manager also stops running, so you will need to boot the PC in Safe mode.
The ransom window cannot be closed like regular program windows. In order to get rid of the ransom warning, you have to end the process of the infection.
As regards the ransom money, the attackers want to receive the payment in Bitcoin, which is a digital currency used anonymously. Over the last few years, cyber criminals have gained substantial sums of money from ransomware victims. You should resist the temptation to pay the ransom. The authors of the Bud ransomware care only about earning money, and you are just one of the many affected by their attack.
In order to remove the Bud ransomware, or any other dangerous threat, it is advisable to rely on a reputable malware removal tool. But if you feel the need to try removing this infection manually, follow the step of our removal instructions given below. Bear in mind that you terminate the infection at your own risk, and any damage caused to the system during manual removal is your own responsibility. In case of any questions regarding the removal of the Bud threat, feel free to comment below.
How to remove the Bud ransomware
- Press Win+R and type in %LOCALAPPDATA% and click OK.
- Go to %LOCALAPPDATA%\Corel\CorelCGS.exe to delete the malicious executable file.
- Press Win+R and type in %APPDATA% and click OK.
- Go to %APPDATA%\Corel\RegisterCGS.exe to delete the malicious executable file.
- Press Win+R and type in regedit. Click OK.
- Delete RegisterCGS.exe after following the path HKCU\Software\Microsoft\Windows\CurrentVersion\Run::RegisterCGS.exe.
Bud Ransomware Screenshots:
Bud Ransomware technical info for manual removal:
Files Modified/Created on the system:
| # | File Name | File Size (Bytes) | File Hash |
|---|---|---|---|
| 1 | RegisterCGS.exe | 484352 bytes | MD5: 3c88518636144a54879a006dc280c8fb |
| 2 | CorelCGS.exe | 484352 bytes | MD5: 3c88518636144a54879a006dc280c8fb |
Memory Processes Created:
| # | Process Name | Process Filename | Main module size |
|---|---|---|---|
| 1 | RegisterCGS.exe | RegisterCGS.exe | 484352 bytes |
| 2 | CorelCGS.exe | CorelCGS.exe | 484352 bytes |

