Anubi Ransomware Removal Guide
Anubi Ransomware is a new ransomware that appeared on 13 of October 2017. However, there is little to no information on how it is distributed. It was designed to encrypt your files and then demand that you pay a ransom to get them back. You should not trust cybercriminals to keep their word, so you ought to remove this program using an anti-malware program or the manual removal guide presented below. In this article, we will provide you with information such as this program’s functionality, possible distribution methods, and removal methods, so if your PC has become infected with it, please continue reading.
Since this ransomware was released only recently, there is little to no information on how its developers distribute it. Nevertheless, we assume that it might be distributed via email disguised as an invoice or some other document that would infect your PC the moment you open that fake document. Also, it could be distributed using insecure RDP connections. Lastly, it could be bundled with pirated software and put up on shady pirated content hosting websites or torrent sites. We have also found that this ransomware does not create a copy of itself anywhere on your PC. Furthermore, one person claims that Anubi Ransomware is dropped in %HOMEDRIVE% and the name of its executable file is locker.exe. Once it is launched, it creates a Point of Execution (PoE) registry subkey named "Adobe Acrobat Optimizer x86" in HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run which will execute locker.exe on each system startup.
Once on your computer, Anubi Ransomware will start encrypting your files, and it will do that each time you boot up your computer. We do not know how this ransomware encrypts your files, but it is likely that it uses either the AES or RSA encryption method or even a combination of both. It should create a private decryption key that it should send to its server, so not to store it locally to be found and used for decrypting your files for free. The list of encrypted files includes your documents, pictures, videos, audios, and so on. All of the encrypted files receive a ".[anubi@cock.li].anubi."
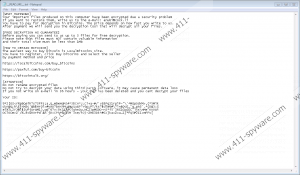
Once the encryption process is complete, Anubi Ransomware is set to drop a ransom note into each folder where files were encrypted. The note is a text file named "__READ_ME__.txt." The note says that you need to pay a ransom in Bitcoins to decrypt your files. The sum of money you have to pay is not specified as it is probably revealed after you contact the criminals via the provided anubi@cock.li email address. You can send the criminals three files that are no larger than 3 MB to be decrypted for free as proof that the criminals mean it when they say they will decrypt your files.
That is all of the information we currently have on Anubi Ransomware. Since it has been released only several days earlier, not all relevant information has surfaced and more time is needed for dissecting and testing the executable. Nevertheless, it can encrypt your files, but you should not trust its developers to decrypt your file once you have paid. We recommend you get an anti-malware program such as our featured program SpyHunter or use the manual removal guide below, but take note that the location of this ransomware is subject to change.
Manual Removal Guide
- Press Windows+E keys.
- Type %HOMEDRIVE% in the address box and press Enter.
- Locate locker.exe, right-click it and click Delete.
- Close File Explorer.
- Press Windows+R keys.
- Type regedit in the box and hit Enter.
- Go to HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- Find Adobe Acrobat Optimizer x86, right-click it and click Delete.
- Close Registry Editor.
- Empty Recycle Bin.
Anubi Ransomware Screenshots:
Anubi Ransomware technical info for manual removal:
Files Modified/Created on the system:
| # | File Name | File Size (Bytes) | File Hash |
|---|---|---|---|
| 1 | __READ_ME__.txt | 1449 bytes | MD5: ebe9358e6efc8a4d56ad6fcf36ed745e |
| 2 | Anubi Ransomware.exe | 55808 bytes | MD5: 418da7a795c80e45775f822098e1e85b |
Memory Processes Created:
| # | Process Name | Process Filename | Main module size |
|---|---|---|---|
| 1 | Anubi Ransomware.exe | Anubi Ransomware.exe | 55808 bytes |

