AES-NI Ransomware Removal Guide
AES-NI Ransomware is a new severe threat that can take your precious files hostage and push you to pay a certain amount of ransom for your files to be released. Such a malicious attack can be a nightmare if you do not have backups saved on a portable drive because you may never be able to use your photos, videos, audio files, text files as well as your archives again. Our research indicates that this infection could be related to a very similar previous threat called AES256 Ransomware. It is practically impossible to realize that your computer has been hit with this malicious program because it infects without your knowledge. Of course, you may have realized that you cannot open your files or that there are questionable .txt files related to this attack appearing in affected folders. In any case, the encryption may take as little as one single minute, which does not really give you enough time window to act against this ransomware. In a way you are lucky, because you do not really need to remove AES-NI Ransomware yourself because this is one of those rare infections that take care of it after the encryption. Still, it is important for you to be able to identify all related files and remove them all from your system before you restart your machine. Please read our full report to learn more about this dangerous threat and how you could avoid such attacks in the future.
Most of the ransomware infections we have seen so far are usually spread in spamming campaigns. We cannot confirm that this particular threat is distributed in this way but it is still essential that we mention other possibilities. You may get an e-mail that sounds a bit doubtful to you; yet, you may want to check it out and open the attached file, which is a malicious .exe file disguised as either a video, an image, or a text document file. When you run this file, it infects your system and the encryption becomes inevitable. Such a spam may claim to be regarding an unpaid invoice, a problematic hotel room booking, wrong credit card details in an online purchase, and other similar issues that would draw your attention right away even if you know that it cannot be related to you personally. Another possible channel for cyber criminals to spread ransomware infections is to set up malicious webpages using so-called Exploit Kits (e.g., Angler). In such an attack you land on this malicious page by clicking on a corrupt third-party ad or a link on a modified search results page. These can be presented to you by malware infections, such as adware programs and browser hijackers, but it is also possible that you are viewing shady websites (torrent, freeware, and gaming) filled with questionable third-party content.
Nevertheless, the most likely way for this ransomware to show up on your server is that the criminals who authored it try to use brute force to access it and activate this infection. This is usually possible when your server is not protected with a decent password or security software and there is a remote desktop software operating on it, which could serve as an open door to cyber criminals. In addition to this, there is another hacking tool that could be responsible for the distribution of this threat. DoublePulsar is one of these NSA tools that have been released to the public lately; or rather, leaked. Obviously, you need to make sure that your server and your computer or computers are all protected properly with professional software and hard-to-crack passwords so that you can prevent such a nightmarish hit from happening. But no matter how this infection has managed to infiltrate your system, in the end, we recommend that you delete AES-NI Ransomware right away.
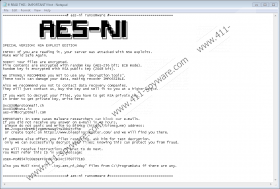
This infection seems to employ the widely used tactics to encrypt your files with an uncrackable recipe of algorithms. First, your files are encrypted with AES-256 algorithm and get a new extension ".aes_ni_0day" then, the generated decryption key is encrypted with RSA-2048. The private key then is stored on a secret remote server. This ransomware also modifies your Windows Registry by creating a new value name in the Winlogon registry key. This value name contains the ransom note text that will be displayed to you every time you try to restart your machine and try to log in. Apart from this, a ransom note text file named "!!! READ THIS - IMPORTANT !!!.,txt" is also placed in each infected folder to make sure that you know what to do after this hit.
This ransom note informs you about the encryption and that you should not try to recover your files or delete AES-NI Ransomware because you could lose all of your important files. You have to send an e-mail to either 0xc030@protonmail.ch, 0xc030@tuta.io, or aes-ni@scryptmail.com with your ID you can find in this note. When you get a response, you will know how to proceed. As of yet, we cannot confirm the amount these crooks demand from you. This can be anything from 100 USD to 1,500 USD worth of Bitcoins or even more. And, sometimes it can also be less when it is a trial run or the work of amateurs. Keep in mind that it is always risky to contact criminals. It is possible that they send you a key or a tool but that could bring more infections to your system and more damage if it is possible at all. In any case, we suggest that you remove AES-NI Ransomware as soon as possible.
If you want to handle this threat yourself manually, you can use our instructions below. Fortunately, you do not need to spend time trying to identify the malicious .exe file that was silently installed on your system since it has been removed automatically. But there is still some mess to clean up. If this vicious program managed to sneak onto your system, there could be other threats also hiding on your PC, not to mention possible future attacks. If you are looking for a powerful way to defend your computer, we advise you to install an authentic anti-malware program, such as SpyHunter. This security software can automatically filter out and remove all known malicious programs and potential threats.
Remove AES-NI Ransomware from Windows
- Tap Win+R and enter regedit. Press OK.
- Delete HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\LegalNoticeText registry value name.
- Exit the Registry editor.
- Tap Win+E.
- Bin all ransom note text files dropped in the affected folders.
- Empty your Recycle Bin and reboot your PC.
AES-NI Ransomware Screenshots: