Searchincognito.com Removal Guide
When you find Searchincognito.com in your browsers, you should ask yourself this question: Do I want to risk my virtual security? As a matter of fact, we have classified this infection as a browser hijacker since it has the ability to change certain browser settings. We do not claim that this happens without your knowledge but it may well happen that you do not realize it. The installers of such extensions can be quite misleading to make sure that you install them with all additional changes and tools. Although there are official channels to download this browser hijacker, we believe that more users get infected with it via freeware bundles. This means that it is possible that you will find several other malware infections on your computer, too. These could put your operating system under a lot of pressure, not to mention the fact that this browser hijacker may also expose you to potentially unsafe web content. That is why we recommend that you delete Searchincognito.com if you want to protect your PC from more infections.
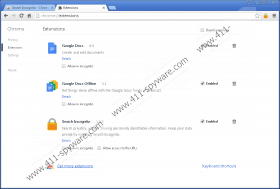
One of the main official sources to install this useless tool is the Chrome web store. You can find this extension at chrome.google.com/webstore/detail/search-incognito/fdobakplmmicnnhioedbifobmpoaglac. However, if you care to have a look at the reviews there, you may change your mind quickly. It becomes quite obvious that a lot of users complain about this extension and they also express their will to remove Searchincognito.com. This makes this browser hijacker questionable even if you have not tried to use it yet. In all fairness, we also need to mention that the publisher do seem to care about the reviews because there are a number of comments they leave when users ask a question or just send a remark. But it still will not make this a useful and reliable tool.
If you want to make sure that you are installing a reliable application, we recommend that you run a web search first. For example, if you use the unique Chrome ID of this extension (fdobakplmmicnnhioedbifobmpoaglac) and run it in Google, you will find a number of articles among the results that explain why you should remove Searchincognito.com. This should already be quite suspicious and a red flag that signals a big no-no if you want to go on installing this application.
Another suspicious thing about this browser hijacker is that it may also be found bundled with other malicious software installers. If you have been visiting unfamiliar file-sharing websites lately, it is possible that you clicked on content that you should not have. These sites are full of unreliable third-party ads that are mostly disguised as something else. Thus, you may think that you click on a download button or a next-page button, but, instead, you download a malicious bundle. It is possible that such a package installs itself automatically in the background so that you will not even know what happened. But it is quite common that you need to run the installer. If that is the case, there is usually an opportunity for you to opt out of the installation of undesirable components. However, this is the step that most users usually skip. That is why they think that they have been infected in some mysterious ways, but, in reality, they themselves triggered the infections. If you are not sure how this annoying browser hijacker entered your computer, you should run a malware scanner on your system right after you delete Searchincognito.com.
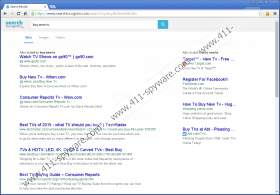
This extension offers you private search without sharing personally identifiable information; however, we have found that this tool is not necessarily reliable. Upon install, this hijacker sets itself as your new default search engine in all major browsers excluding Edge. It also sets the new home page in Internet Explorer to Searchincognito.com. It is possible that this hijacker may start showing third-party advertisements, which is actually revealed in its Terms of Service. This application belongs to the minority of browser hijackers that use their own search engines to display results. However, these results may not always be trustworthy. Since cyber criminals can take advantage of such low-security applications, it is possible that they inject their own advertisements and sponsored links through this hijacker, too. This way, you may encounter potentially unsafe ads and links on the search results pages. Clicking on such content may redirect you to suspicious websites, which, of course, hold certain unwanted risks. Reports also show that these results may take a bit longer than usual to load and the quality of the links may not be the best either. All in all, we do not advise you to use this extension. On the contrary, we suggest that you remove Searchincognito.com as soon as possible.
Although this tool has an uninstaller that you can run through Control Panel, it seems that it only takes care of the Internet Explorer browser. If you want to undo all the changes in the rest of the browsers, you should do so manually. We recommend that you reset your browsers in order to start with a clean slate. Please follow our instructions below if you need assistance with the required steps. If you want efficient protection against malware intruders, you should consider the installation of an up-to-date malware removal application.
How to remove Searchincognito.com from Windows
Windows XP
- Access the Start menu and go to Control Panel.
- Pick Add or Remove Programs.
- Click on the application and press Remove.
Windows Vista and Windows 7
- Press Win+R and type in Control Panel. Press OK.
- Select Uninstall a program.
- Click on the application and press Uninstall.
Windows 8, Windows 8.1, and Windows 10
- Press Win+X and choose Programs and Features.
- Click on the application and press Uninstall.
Reset your browsers
Google Chrome
- Press Alt+F and go to Settings.
- Click Show advanced settings at the bottom.
- Click Reset settings at the bottom.
- Press Reset.
Mozilla Firefox
- Press Alt+H and choose Troubleshooting Information.
- Press Reset Firefox at the top.
- Click Reset Firefox in the confirmation window.
- Click Finish.
Searchincognito.com Screenshots: