HydraCrypt Ransomware Removal Guide
HydraCrypt Ransomware is a serious computer infection that might slither onto your computer one day. As this threat needs the Internet connection to enter systems, people who do not use Internet are not likely to encounter this infection. Do you surf the web on a daily basis? If so, there is a huge possibility that this threat will cause harm to your system one day. We are sure that you will notice that because you will not be able to access any of your files anymore. In addition, a message with red borders will be put on your desktop. Luckily, it will not block your screen and you will be able to access your desktop. Even though HydraCrypt Ransomware does not block .exe files and system utilities, it is still not easy to remove it. Besides, it will not disappear after the system restart because this ransomware infection applies changes to the system registry that allow it to launch the moment Windows OS loads up. It is not an easy task to do that, but you still have to eliminate HydraCrypt Ransomware from the system. It is especially true if you are going to recover files encrypted by HydraCrypt Ransomware from a backup.
Yes, you have understood correctly - HydraCrypt Ransomware is going to encrypt all the files. Specialists working at 411-spyware.com have managed to find out that it is mainly interested in various images, documents, videos, and music files with the following filename extensions:
.bin, .bk, .bmp, .cfg, .dat, .db, .doc, .docx, .gif, .gz, .htm, .html, .ini, .jpeg, .jpg, .js, .mp3, .mp4, .pdf, .png, .ppt, .pptx, .sdf, .tmp, .txt, .wma, .wmv, .xls, .xlsx, .xml
It is not hard to recognize those encrypted files because this infection will add a unique ID that consists of 8 numbers to all of them, for example, it will change example.file into example.file.hydracrypt_ID_(8 unique numbers). Of course, another symptom that they are encrypted is the inability to open any of them.
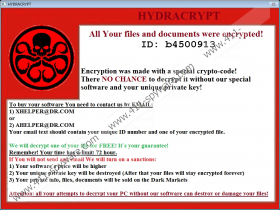
After HydraCrypt Ransomware finishes encrypting all the files, this threat will put a message on the screen. If you see such a message (see an excerpt below), you can be sure that you have become a victim of this ransomware infection:
Encryption was made with a special crypto-code!
There NO CHANCE to decrypt it without our special software and unique private key!
If you already see it, you definitely know what you have to do next, i.e. to contact cyber criminals by one of the given emails (XHELPER@DR.COM or AHELPER@DR.COM). We are sure that you will be sent further instructions on how to pay a ransom. Like other ransomware infections, it will, most probably, ask you to pay money in Bitcoins, and it will give you a limited period of time (72 hours). HydraCrypt Ransomware tries to scare users into paying money, so it says that it will destroy the unique key and sell your files on the black market if you do not send money. It sounds rather scary; however, there are no guarantees that you will receive software for unlocking your files after making a payment. You are the only one who can decide what to do, but we believe that it would be best to restore files from a USB flash drive or another backup. Do not forget to eliminate HydraCrypt Ransomware first!
Researchers have managed to find out that HydraCrypt Ransomware needs 10-20 minutes in order to encrypt all the files existing on the system. In order not to be removed during this time, it creates a copy of itself and puts it into one of the following directories: %APPDATA%, %LOCALAPPDATA%, and %TEMP%. It has been observed that the name of its executable file consists of 7-10 letters. In order not to be removed easily and not to disappear after the system reboot, HydraCrypt Ransomware will also create and add two Values to the system registry. One of these Values might have a name ChromeSettingsStart3264. You will find it if you access the Registry Editor and then follow this path: HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run. Last but not least, it has been observed that HydraCrypt Ransomware pretends to be a useful application, e.g. an image viewer in order not to be recognized and deleted. As can be seen, this ransomware infection seeks to stay on the system by any means.
HydraCrypt Ransomware is spread in a similar manner if compared to other ransomware infections, e.g. 7ev3n Ransomware, CryptoJoker Ransomware, and Radamant ransomware. In other words, users download it after they open an infectious spam email attachment mainly; however, this threat might also enter the system if users tend to download various programs from third-party web pages and click on links available on untrustworthy pages. The entrance of HydraCrypt Ransomware might also be the result of the presence of other malware. Finally, it is targeted at those computers which are unprotected.
It is a must to delete HydraCrypt Ransomware from the system if you are going to restore files from a backup and are not planning on paying money for cyber criminals. It will not be very easy to do that, so we suggest following our manual removal instructions step by step. In case you are not experienced enough to eliminate this threat yourself, scan your system with an automatic antimalware scanner, such as SpyHunter. It will eliminate all the existing infections for you and then will make sure that they cannot enter your system again.
Remove HydraCrypt Ransomware from your computer
Display hidden files and folders
Windows XP
- Open the Start menu and click Control Panel.
- Select Appearance and Themes.
- Click Folder Options and then open the View tab.
- Mark Show hidden files and folders.
- Click OK.
Windows 7/Vista
- Go to Windows Explorer.
- Click on the Organize tab.
- Select Folder and search options and open the View tab.
- Mark Show hidden files, folders, and drives.
- Click OK.
Windows 8/8.1/10
- Tap the Windows key + E on your keyboard.
- Click on the View tab at the top and select Options.
- Open the View tab.
- Enable Show hidden files, folders, and drives.
- Click OK.
Remove the ransomware infection
- Type regedit.exe into the Search box.
- Right-click on it and select Run as administrator.
- Move to HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run.
- Delete Values (e.g. ChromeSettingsStart3264) associated with HydraCrypt Ransomware.
- Close the Registry Editor and go to Windows Explorer (Windows key + E).
- Locate the file whose name consists of random letters in %APPDATA%, %LOCALAPPDATA% or %TEMP%. Delete it.
- Remove two images of HydraCrypt Ransomware placed together with it.
- Remove files that belong to the ransomware infection from your Desktop.
- Empty the Recycle Bin.
- Reboot your PC.
HydraCrypt Ransomware Screenshots: