RanRans Ransomware Removal Guide
If RanRans Ransomware slithered in, the chances are that you executed the malicious launcher of this infection by opening a file attached to a misguiding spam email. At the time of research, this infection was not spreading very noticeably, but that does not mean that this would not change. Overall, it is unlikely that this threat will perform mass attacks because that is not what we see Hidden Tear ransomware doing. Other threats that belong to this family include Unikey Ransomware, SucyLocker Ransomware, and Kindest Ransomware, and while they might have been created by different parties, they all were created using the same open source code. Unfortunately, anyone with basic knowledge can use it to build their own infections. There is only one purpose for this malware, and that is to make users pay a ransom, which, in this case, is 50 USD. Although the sum is quite small in comparison, it must be pointed out that this ransom is unlikely to be swapped for a decryptor. To learn more, including how to delete RanRans Ransomware, continue reading this article.
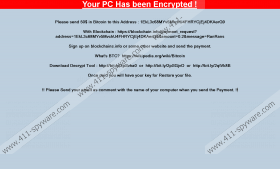
Once the malicious RanRans Ransomware is activated, it does not create any files. It does not even create a copy of itself, which is what most infections of this kind do to stop victims from removing them. Instead, it connects to https://ranrans.000webhostapp.com/write.php?info= (C&C server) and then immediately initiates the encryption. The files are encrypted using the AES encryption key, and you need a decryption key to recover them. To make it more obvious which files were corrupted, the devious infection attaches the “.ranrans” extension to their names. The sample we tested encrypted data in %ALLUSERSPROFILE% and %USERPROFILE% folders and sub-folders. Unfortunately, not all users know this because the ransomware locks the screen using a screen-size notification entitled “Your PC Has been Encrypted!” Obviously, it is not your computer that was encrypted, but the personal files found on it. If you want to see which files were encrypted, you can follow the instructions below that show how to unlock the PC. Note that once you unlock it, the ransom note will disappear for good. That, however, does not mean that RanRans Ransomware is removed as well.
The screen-locking notification used by RanRans Ransomware suggests that the victim must register a Bitcoin Wallet with blockchain.info and then send a ransom of 50 USD converted to Bitcoins to 1EkL3c68MYv5MvchU4FHRYCjEj4DKAerG9. As we mentioned before, this threat does not spread on a high scale yet, and so it is not surprising that no one has transferred any money to this Wallet yet. When you visit the blockchain.info link that is shown in the ransom note, you are then asked to transfer a ransom of 0.2 BTC, which, at the time of research, was around 460 USD. As you can see, it is not clear how much exactly you are expected to pay. Overall, paying is not an option because the Decryption Tool does not exist. Our research team has found that the installer of this alleged tool does not exist on any of the three sources that are presented via the ransom note. Even if this tool existed, it is unlikely that cyber criminals would give you the decryption tool that worked anyway. What does not mean? Well, that means that if you do not have backups of the encrypted files, you might have lost them.
You need to remove RanRans Ransomware from your operating system. Even if it does not encrypt your files again, and its elimination will not save the encrypted files, this infection is dangerous because it can communicate with a remote server, which makes it a true ticking bomb. The instructions below show how to delete this ransomware manually step-by-step, but you should not rush to follow them. First, think if maybe you should install a reliable anti-malware tool instead. This tool can be very useful if other infections besides RanRans Ransomware are running on your PC. If they are, they will be erased automatically. The second thing you need to think about is the protection of your operating system. You must realize by now how easy it is for malware to slip in unnoticed. If you want to avoid that, you definitely need the help of legitimate anti-malware software.
How to delete RanRans Ransomware
- Tap Ctrl+Alt+Delete and select Start Task Manager.
- Identify the malicious process representing the ransomware (check the Description and the information in the Properties to identify the right process) and right-click it.
- Click Open File Location to open the folder representing the malicious .exe file linked to the process.
- In the Task Manager, click the process once and then choose End Process/Task.
- Exit Task Manager and then Delete the malicious .exe file.
- Empty Recycle Bin and then immediately run a full system scan.
RanRans Ransomware Screenshots: