Wana Decrypt0r Ransomware Removal Guide
Wana Decrypt0r Ransomware also known as WannaCry Ransomware is a malicious threat that infected a lot of computers around the world by exploiting a particular Windows vulnerability. It seems the vulnerability of Microsoft operating systems was already noticed some time ago and there was even a patch released to fix it, but not everyone got their systems updated in time. Users are urged to upgrade their systems even now when Wana Decrypt0r Ransomware is no longer being distributed. The malware is both a worm and file-encrypting program, so it encrypts private data located on the infected computer. Sadly, at the moment the threat remains to be non-decryptable; thus, if you have no copies from which you could recover damaged files, there is not much do to but to hope the volunteer IT specialists will create a decryption tool. As for now, we recommend erasing the malicious application since leaving it unattended could be dangerous. If you need manual deletion instructions, slide below and follow our provided steps.
The worm should place particular files on the system before it starts encrypting your data. First of all, the malware is supposed to create an executable file called tasksche.exe in %WINDIR% folder. The file’s copy might be placed in a randomly titled folder set up in the %ALLUSERSPROFILE% or %ALLUSERSPROFILE%\Application Data directory. Other files belonging to Wana Decrypt0r Ransomware are placed only after the infection finishes encrypting user’s personal data, e.g. photos, videos, various documents, and so on. There are 151 different extension on the malicious application’s targeted extensions list, which means it can damage quite a wide range of different file types. Users can easily separate the threat’s encrypted data by taking a look at the files name. If it has a second extension called .WNCRYT or .WNCRY, there is no doubt such data is no longer usable.
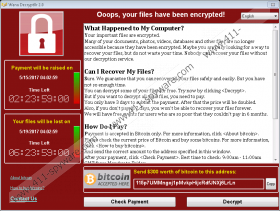
Soon after marking all your files with the mentioned second extension the malware should drop the @WanaDecryptor@.exe file in every folder containing encrypted data. The file opens the same pop-up message the infection launches automatically. Additionally, Wana Decrypt0r Ransomware should place a text document version of the ransom note (@Please_Read_Me@.txt); it might be created in each directory with damaged data as well. As expected the pop-up message demands you pay the ransom if you want to decrypt your files. The malicious application’s creators even guarantee you will be able to do so once they receive the money. The problem is, there are no refunds, and if something goes wrong, you might be left without a decryptor and the money you transferred to the cyber criminals. Therefore, we advise you not to put up with any demands and get rid of this worm.
After the malware is eliminated and the system is secure, you could upload copies of damaged files from removable media devices or other storages. Also, there are various recovery tools you could try to get back at least some of the encrypted files. To erase Wana Decrypt0r Ransomware manually, users should follow the deletion steps provided below the text. However, keep it in mind the worm is a dangerous threat, so removing it manually could be rather complicated. What we mean is it might be best to use a reliable security tool instead. Once the malicious application is eliminated, you should keep the antimalware tool on the system as it might prove to be useful in the future too. Juts keep it updated so it could fight newer threats as well.
Reboot the device in Safe Mode with Networking
Windows 8/Windows 10
- Press Windows Key+I and tap the Power button.
- Hold the Shift key and press Restart at the same time.
- Choose Troubleshoot and select Advanced Options.
- Pick Startup Settings and click Restart.
- Press the F5 key and restart the system.
Windows XP/Windows Vista/Windows 7
- Click Start, select Shutdown options and press Restart.
- Keep pressing the F8 key right after the computer starts restarting until you see the Advanced Boot Options window.
- Select Safe Mode with Networking and click Enter.
- Log on to the computer.
Remove Wana Decrypt0r Ransomware
- Press Windows key+E.
- Check your Temporary Files, Downloads, and Desktop directories.
- Locate the suspicious file that might have been downloaded and opened when the system got infected.
- Right-click this infected file and select Delete.
- Go to %WINDIR%
- Find a file named as tasksche.exe.
- Right-click it and choose Delete.
- Look for these locations:
%ALLUSERSPROFILE%
%ALLUSERSPROFILE%\Application Data - Search for randomly named folders containing the tasksche.exe file.
- Right-click these malicious folders separately and select Delete.
- Erase the @WanaDecryptor@.exe files and @Please_Read_Me@.txt files by right-clicking them and selecting Delete.
- Exit the Explorer.
- Empty your Recycle Bin and restart the computer.
Wana Decrypt0r Ransomware Screenshots: