Sigma Ransomware Removal Guide
According to our specialists, users might receive Sigma Ransomware after opening malicious software installers. Afterward, the threat should lock private data located on the computer with strong encryption algorithms called AES and RSA. Sadly, deciphering data is only possible if you have a decryption tool and a unique decryption key generated by the malware. The cyber criminals behind Sigma Ransomware claim they have such tools and promise to deliver them if the user pays a ransom. The problem is that the asked sum is not a small one, and there are no guarantees the hackers will keep up with their promise. This is why we believe it would be safer to pay no attention to their demands and erase the threat. Later, users who have backup copies could restore enciphered data. As for more information on this infection, read the rest of our text.
The malware might encrypt various data, e.g., pictures, photos, videos, archives, music files, text documents, and more. It was noticed the malicious program does not use the same extension for all infected devices but generates a unique extension to mark each victim’s data differently. Apparently, Sigma Ransomware’s extension should be generated from 4 random characters. For instance, a file called video.avi could look like video.avi.82NA on one computer and video.avi.wDn9 on another one, and so on.
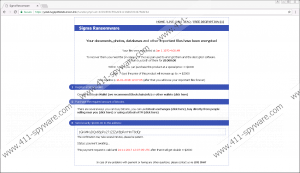
Soon after the malicious program finishes enciphering user’s data, it should create a couple of files on the Desktop directory and folders with encrypted files. The mentioned files should be called ReadMe.txt and ReadMe.html. Both of them are supposed to give the user message from the cyber criminals who created Sigma Ransomware. For example, one of it starts with a question: “What has happened to my files ? Why i am seeing this ?” and answers it by saying “All of your files have been encrypted with RSA 2048 Encryption. Which means, you wont be able to open them or view them properly. It does NOT mean they are damaged.” The files might not be actually damaged, but if the user does not have the means to restore them, they are ruined to him forever.
Furthermore, the malware’s ransom note not only explains what happened to the user’s files but also gives instructions on what he should do to get “a decrypter along with your private key.” It looks like the hackers want users to make a payment of $1000 or $2000 if they do not pay the ransom in a week. Comparing it to the sums asked by other malicious program’s alike, it seems rather huge, and since no one cannot be certain, the cyber criminals have the promised decryption tools we do not think it would be a good idea to gamble with your savings. Instead, we would advise concentrating on the malware’s deletion.
Sigma Ransomware can be eliminated manually, and if you feel up to such a task, you should follow the instructions located below the article. For less experienced users it might be easier to install a reliable antimalware tool, run a system scan, and delete the malicious program by clicking the removal button. Not to mention this way you would strengthen the system and could get rid of other possible threats at the same time.
Remove Sigma Ransomware
- Press Ctrl+Alt+Delete.
- Open Task Manager and click on Processes.
- Find a process related to the malware.
- Click it and tap the End Task button.
- Exit Task Manager.
- Click Win+E.
- Check the Desktop, Temporary Files, and Downloads locations.
- Identify the threat’s launcher.
- Right-click the file you suspect and tap Delete.
- Locate and erase all ransom notes (ReadMe.txt and ReadMe.html).
- Close File Explorer.
- Empty Recycle bin.
- Reboot the system.
Sigma Ransomware Screenshots:


Sigma Ransomware technical info for manual removal:
Files Modified/Created on the system:
| # | File Name | File Size (Bytes) | File Hash |
|---|---|---|---|
| 1 | Sigma Ransomware.exe | 3207826 bytes | MD5: 674936a2beb25def88db410f3d1b68de |
| 2 | ReadMe.html | 3669 bytes | MD5: 9f204712b5d6c5a930182a57eb2decd8 |
Memory Processes Created:
| # | Process Name | Process Filename | Main module size |
|---|---|---|---|
| 1 | Sigma Ransomware.exe | Sigma Ransomware.exe | 3207826 bytes |

