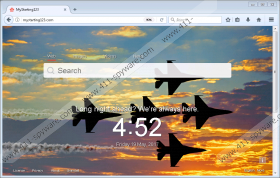
Mystarting123.com Removal Guide
Mystarting123.com might be one of the Elex family browser hijackers. Usually, threats alike change user’s default start page to encourage him to browse with the unreliable search engine. As a result, the application might be able to collect information about the user’s browsing habits or other details, e.g. visited web pages, used keywords, purchased goods, location, etc. This data could be shared with the software’s third-party associates to bring you targeted ads. The problem is, while the advertisements may look tempting, they could originate from harmful web pages. In other words, users who click ads from the browser hijacker’s third-party partners could be redirected to malicious websites dangerous to the system or your privacy. Naturally, such content might make browsing with Mystarting123.com quite risky; therefore we would advise you to find a more reliable search tool and erase this questionable application at once.
Mystarting123.com might be a clone of other suspicious search engines associated with the Elex family browser hijackers, e.g. MyLuckySearching.com, Myhomepage123.com, Luckystarting.com, and so on. Our researchers have encountered a lot of similar threats over the years and from this experience with them we can say that a lot of similar threats are often being distributed through malicious bundled installers. These setup files can be spread through the so-called P2P websites, other file-sharing web pages where programs might be distributed without their authors’ consent, or sites distributing unreliable freeware applications.
As much as it might seem tempting to get a tool without paying anything at all, keep it in mind that sites distributing stolen applications may bundle their installers with untrustworthy or malicious software. Talking about freeware, it can have exaggerated descriptions, so users should be extremely careful while choosing what to download. If you still plan on using untrustworthy file-sharing web pages even despite all risks, we would recommend downloading a legitimate antimalware tool at least. For as long as it is updated it should be able to notify you about suspicious programs you could be installing and keep the system malware free.
What happens when Mystarting123.com hijacks your homepage? The browser starts loading it each time it is opened. Such behavior might continue even if you go to the browsing application’s settings and set a new start page. That is because the search engine may settle in by altering specific files of your browser. There is a way to restore such data, but we will talk about it in the last paragraph. For now, we would like users to know that if they begin using the browser hijacker for surfing the Internet, they may encounter malicious advertising content from unknown sources. If something like this would happen, we advise you not to interact with these ads as they might lead you to sites containing viruses, worms, ransomware, or other threats. What’s more, it is entirely possible some of the third-party web pages could be invading the user’s privacy or trying to obtain sensitive data through fake surveys, lottery tickets, etc.
The web pages you may get redirected while clicking third-party ads could be dangerous for other reasons as well and although we cannot be more precise about these risks, we advise you to eliminate Mystarting123.com in order to avoid them. To delete the browser hijacker manually, you should restore the threat’s altered files. If you take a look at the steps located below this paragraph, you will learn how to find the possibly modified data and how to fix it. Users who find this process a little bit too complicated could simply acquire a reliable antimalware tool and let it handle this unreliable search engine.
Erase Mystarting123.com
Internet Explorer
- Press Win+R.
- Type Regedit and click Enter.
- Find a value name called Start page in the given location: HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main
- Right-click it and choose Modify.
- Replace the browser hijacker’s link (http://Mystarting123.com) and press OK.
- Exit Registry Editor.
Mozilla Firefox
- Click Win+E.
- Locate file named as prefs.js in the listed directory: C:\Users\user\AppData\Roaming\Mozilla\Firefox\Profiles\{unique user ID}
- Open this file as a Notepad document.
- Find a line containing the threat’s link: user_pref(“browser.startup.homepage”, “http://Mystarting123.com”).
- Replace http://Mystarting123.com and press Ctrl+S.
- Exit Notepad.
Google Chrome
- Press Win+E.
- Go to: C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default and find the mentioned files:
Preferences
Secure Preferences
Web Data - Right-click these files separately and select Delete.
- Leave File Explorer.
Mystarting123.com Screenshots: