LockerPay Ransomware Removal Guide
LockerPay Ransomware is a typical ransomware-type computer infection that was designed to encrypt your documents and pictures. Its purpose is to extract money from you, so it will demand you pay money for the decryption key. Now, you should remove this ransomware instead of complying with the cyber crooks’ demands because it is likely that they will not give you the decryption key. There is not much information about this new malware, but we will try to present you with the most relevant information regarding its functionality and distribution. So if your PC has become infected with this particular ransomware, then we kindly invite you to read this whole description.
Let us begin our analysis with how LockerPay Ransomware is disseminated. We have found that this ransomware is distributed via phishing emails. The developers have set up a server dedicated to sending email spam to a preselected list of email addresses acquired through unknown methods. The mails should contain this ransomware’s main executable, but it should be zipped. As a result, the user has to extract the file and run it manually. The file might have a double extension and pose as an MS Office document, PDF file or something of the sort. In the unfortunate event of you extracting and running the malicious executable, this ransomware will start encrypting your files.
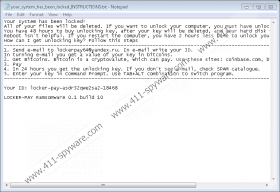
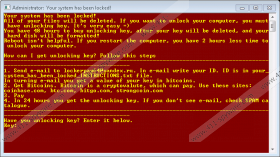
If you run the malicious executable, then it will start encrypting your files immediately. Our research has shown that this particular ransomware targets pictures and documents in particular. Therefore, it is clear that this ransomware is not supposed to damage any system files and corrupt the system’s processes. Hence, you should be able to use your PC post encryption. This program should use either an RSA or AES encryption algorithm, but further analysis is required to confirm this. Like most ransomware, this program should create a public encryption key and a private decryption key. The decryption key should be sent to the primary server and stored until you pay the ransom. LockerPay Ransomware gives you a 48-hour window to buy the decryption key because its ransom note claims that it will delete your files if you fail to meet the deadline. To pay the ransom, you have to contact the cyber criminals via email at lockerpay64@yandex.ru. Once the encryption is finished, lockerpay64@yandex.ru LockerPay Ransomware is set to render a window that features a ransom note. Also, it drops a text file named your_system_has_been_locked_INSTRUCTIONS.txt in each location where a file was encrypted. Furthermore, both ransom notes feature the same text.
We argue that paying the ransom is a bad idea because the cyber crooks might not send you the decryption key even if you pay. Furthermore, the amount you are supposed to pay is not indicated in the ransom note, so it may be revealed to you only when you contact the developers. The ransom might be too high and not worth your files, so you should also take that into count before paying any significant sum of money. If you want to remove LockerPay Ransomware, then you can delete it manually using our guide or get an anti-malware program such as SpyHunter to do this for you.
How to delete LockerPay Ransomware
- Hold down Windows+E keys.
- Type %TEMP% and C:\Users\{UserName}\Downloads in the address box.
- Locate the randomly named executable.
- Right-click it and click Delete.
- Empty the Recycle Bin.
LockerPay Ransomware Screenshots: